Who is Connected to My WiFi ?
In today’s tech-savvy world, Wi-Fi has become an indispensable part of our lives, connecting us to the digital realm and enabling countless tasks. However, this invisible network also poses security concerns, making it crucial to understand who’s connected to your Wi-Fi and taking advantage of your internet access.
Demystifying Wi-Fi Network Connections
Imagine your Wi-Fi network as a bustling city, with devices constantly entering and exiting, consuming bandwidth and potentially jeopardizing your privacy. It’s essential to gain visibility into this digital neighborhood to safeguard your network and ensure its integrity.
Identifying Unauthorized Devices
The first step towards securing your Wi-Fi is identifying any unauthorized devices that might be piggybacking on your connection. These unwanted guests can steal your bandwidth, engage in malicious activities, or expose sensitive personal data.
To uncover these hidden connections, you can either access your router’s admin panel or utilize dedicated Wi-Fi monitoring tools. Router interfaces typically provide a list of connected devices, along with their MAC addresses and device names.
Protecting Your Wi-Fi Sanctuary
Once you’ve identified unauthorized devices, it’s time to secure your Wi-Fi network to prevent further intrusions. Here are some effective strategies:
Change Default Passwords
Most routers come with default passwords that are easily accessible. Replace these generic passwords with strong, unique ones that are difficult to guess.
Enable WPA/WPA2 Encryption
WPA/WPA2 encryption is the industry standard for securing Wi-Fi networks. It scrambles data transmitted over the network, making it unreadable to unauthorized individuals.
Disable Wi-Fi Protected Setup (WPS)
WPS is a convenient feature that allows devices to connect to your Wi-Fi network without entering a password. However, it’s also a security vulnerability that hackers can exploit. Disable WPS to enhance your network’s protection.
How to check connected users
It can be more dangerous than you think , if someone gain access to your network (WiFi Router), because they can access to all the devices and computers on your network. They can access your files, they can infect your computers with malwares, and in certain situations they can even steal your passwords and other personal information.
Fortunately, there are several ways to determine who’s connected to your WiFi network. Most routers have a simple interface that allows you to view connected devices. Simply log in to your router and browse the list of connected devices.
You can also download a network scanner app on your smartphone or computer. This app will scan your network and provide you with a list of connected devices, including their IP addresses and MAC addresses.
There are two methods for checking the Router’s connected devices( Users) , The first method is to use router’s web console and the other is to use third party softwares and Apps.
1- By Using Router’s Console
Most WiFi Routers (Wireless Router) have a brief report for connected users in their web console. You can check the connected users and find their name, IP Address, Mac Address and connection type. Read More: How to Open WiFi Router’s Web Console?
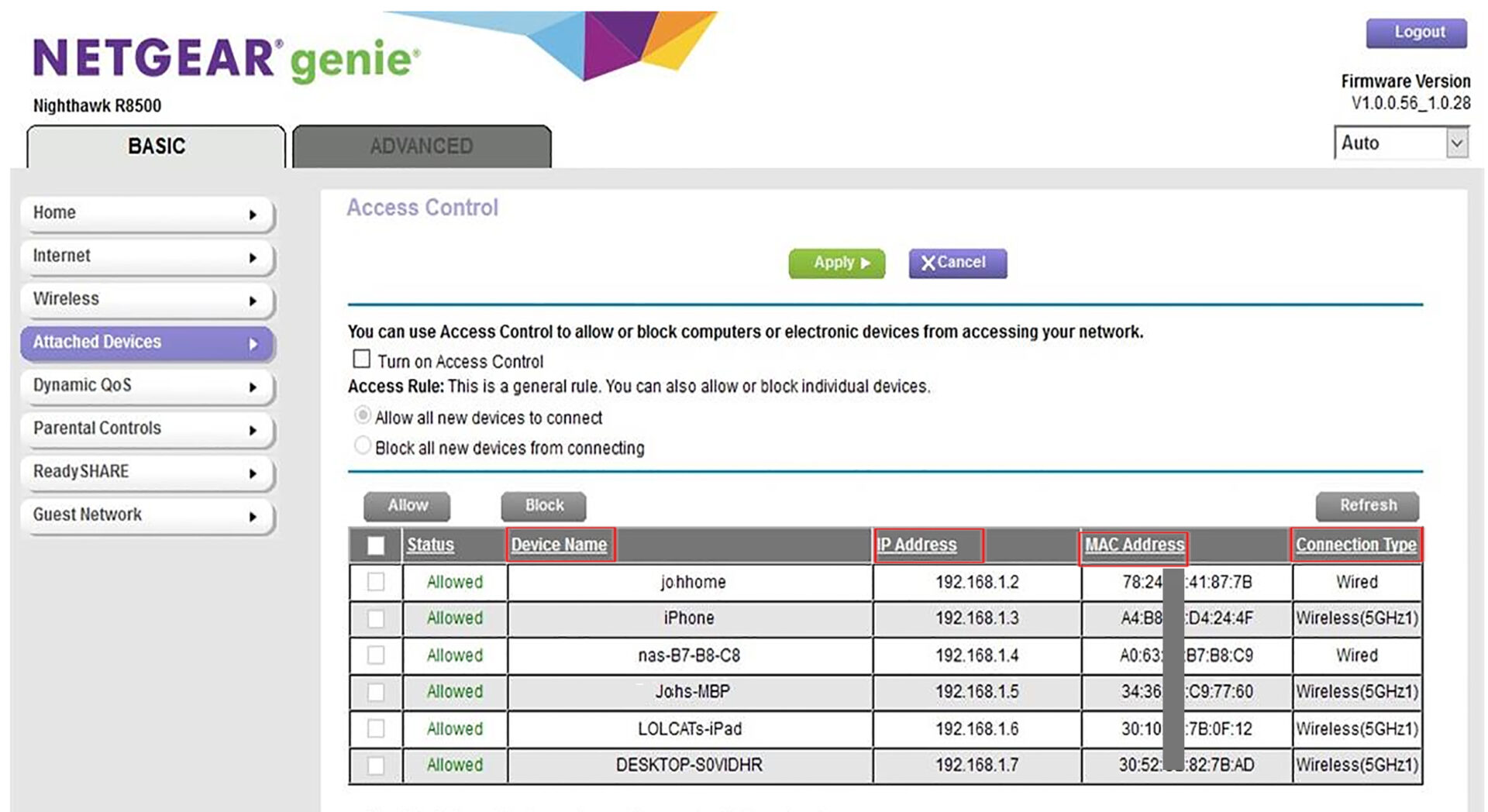
Checking router’s web interface to identify unauthorized WiFi users and protect your network
2- By Using Windows Application
For windows users the “Wireless Network Watcher” is best option. You can run this software on your computer and find all network’s connected users by a simple scan.
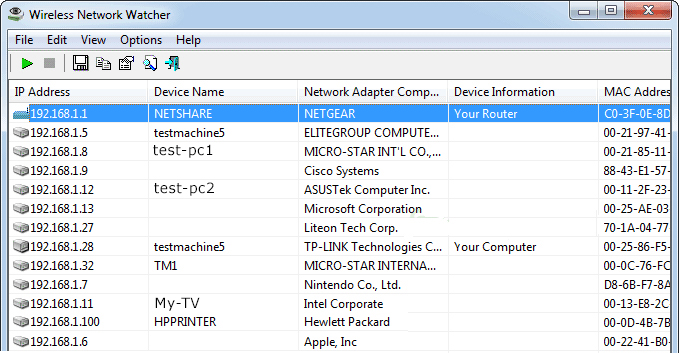
Efficiently monitor your WiFi network and identify unauthorized users with NirSoft’s Windows app
to find more detailed information , double-click on each connected device
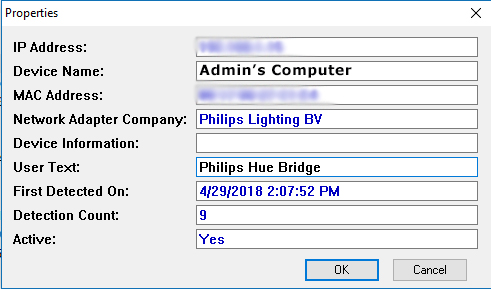
A Wi-Fi network’s Connected Device Information
3- By Using Android App
There are a few android App’s for checking the connected devices. I prefer to use “Home WiFi Alert” app. This app displays the connected devices, WiFi signal info, IP addresses, MAC addresses, Vendor names ,speed, etc.
Read More: How to Extend WiFi Range
One of the impressive options of this App is Blacklist IP Address feature, which helps you to remove the specified connections and block the specific IP address.

Secure your WiFi network from unauthorized access with the Home WiFi Alert Android app
4- By Using iOS App
With iNet App , you can have a real-time monitoring system. Which shows the devices connected to your Wired and wireless network, with detailed information such as their name, IP address, and vendor name, even for Hidden devices. Most devices are displayed with their correct icon.
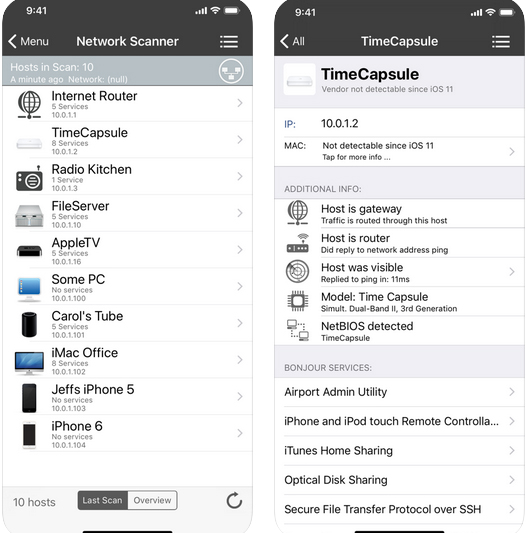
Keep your iOS device’s WiFi network secure with the iNet – Network Scanner
Conclusion
Your Wi-Fi network is a valuable asset, connecting you to the digital world and enabling countless activities. By understanding who’s connected to your network and taking proactive measures to protect it, you can safeguard your internet experience and maintain control of your online privacy. Remember, vigilance is key in today’s interconnected world, where Wi-Fi is no longer just a convenience but a gateway to your digital life.





